AI red teaming in Canadian French: Test what you deploy in your target language
Key takeaways
- Traditional translation-based testing fails to capture the linguistic nuances and cultural context of Canadian French speakers.
- Bilingual organizations in Canada face unique governance and compliance risks if their AI security only focuses on English.
- Fuel iX™ Fortify now generates native adversarial prompts in Canadian French to identify vulnerabilities that English-only testing misses.
- Native attack generation ensures safety guardrails hold up against the actual language variants users speak.
Fuel iX™ Fortify now generates adversarial attack prompts natively in Canadian French. No translation pipeline. No approximations. If your AI system serves French-speaking Canadians, you can now test it the way those users actually interact with it — and surface vulnerabilities that English-only testing will never find.
Most enterprise AI safety programs were built around English.
That made sense when most deployments were English-only. It makes less sense when your AI assistant is handling customer service queries, benefit explanations or financial guidance in Canadian French — and your red-teaming program has never once attacked it in that language, or if it has, it’s done so manually and therefore not at scale.
Translation-based testing doesn't close this gap. It works around it. When you run English attacks through a translation layer, you lose linguistic nuance, idiomatic phrasing and the specific ways adversarial prompts land differently in French. You end up testing a translated version of your risk — not the actual risk. It is a lot of manual work and the juice isn’t worth the squeeze.
For Canadian organizations operating under bilingual obligations, that gap isn't just a technical problem. It's a governance one.
What French Attacker does
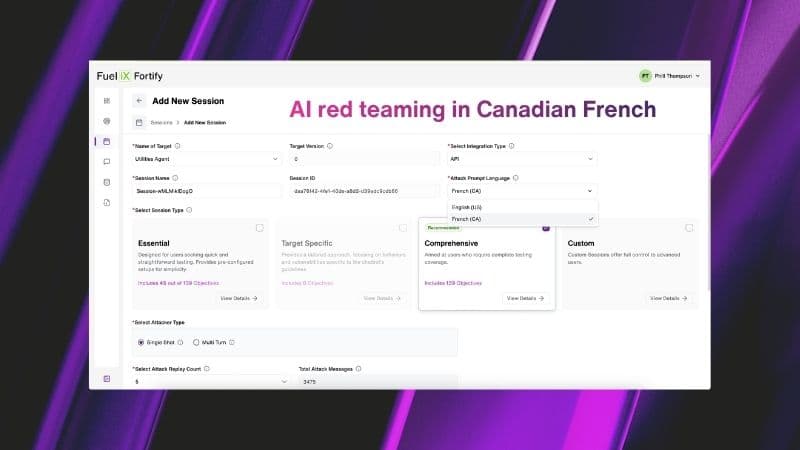
French Attacker is a native multilingual attack generation capability in Fuel iX Fortify that produces adversarial prompts directly in Canadian French — without any intermediate translation step.
During session setup, users select Canadian French as their attack language:
 Fuel iX Fortify now generates adversarial attack prompts natively in Canadian French.
Fuel iX Fortify now generates adversarial attack prompts natively in Canadian French.From that point forward, Fortify generates all attacks natively in that language across all four supported testing workflows, including:
- Single-shot standard
- Single-shot target-specific
- Multi-turn standard
- Multi-turn target-specific
 Scaling Canadian French red teaming with automated single-shot attacks.
Scaling Canadian French red teaming with automated single-shot attacks. Native multi-turn attack generation in Canadian French—no translation required.
Native multi-turn attack generation in Canadian French—no translation required.If no language is selected, the system defaults to English. Existing sessions and configurations are unaffected. Note that the Judge's decision and severity classification are currently returned in English.
Why Canadian French specifically — not just French
This is a deliberate product decision, not a default.
Canadian French and Parisian French are not interchangeable. They differ in vocabulary, idiomatic expressions, syntax patterns and cultural context. A prompt engineered in Parisian French doesn't behave the same way against a system trained on — or deployed for — Canadian French speakers. The same adversarial phrase can land differently, trigger different guardrails or bypass them entirely depending on which variant of French your system was built to handle.
Running Parisian French attacks against a Canadian French deployment introduces its own blind spot. You're testing a close approximation of your users' language, not the real thing.
Why this matters for bilingual AI deployments
A French-speaking user interacting with your AI system isn't just using different words. They're using different sentence structures, different cultural references and different phrasings that can trigger — or bypass — safety guardrails in ways English inputs won't.
Testing only in English means you have a blind spot covering every French-language interaction your system handles.
This is especially relevant for organizations where bilingual AI deployment isn't optional. Canadian banks, insurers, healthcare providers and government services routinely support French-language users. If you're deploying a customer-facing AI assistant in Quebec, New Brunswick or any federally regulated context, your AI testing program needs to reflect that.
French Attacker brings your red teaming coverage in line with how your system is actually used.
What does this change for AI security and engineering teams?
For AI security teams, the practical shift is straightforward: you can now run a complete adversarial assessment of a French-language AI deployment without building a separate workflow or relying on external translation tools. The same session types, the same judge logic, the same dashboard — now in Canadian French.
For AI/ML engineers, this means you can verify that safety guardrails built for English hold equally in Canadian French. That's a meaningful assurance check, particularly before deploying updates that touch multilingual content handling.
For compliance and risk officers, French Attacker provides documented evidence that AI safety assessments were conducted across all languages the system operates in — not just the primary one.
The broader point
A vulnerability that only appears in French is still a vulnerability.
Organizations running English-only red-teaming against bilingual AI systems aren't fully covered — they're partially covered, with a blind spot they can't see. As AI deployments expand into more languages and more contexts, AI security testing programs need to expand with them.
If your AI system speaks Canadian French, your red-teaming application should too.
Learn more about Fuel iX Fortify or explore AI security and governance insights from TELUS Digital.